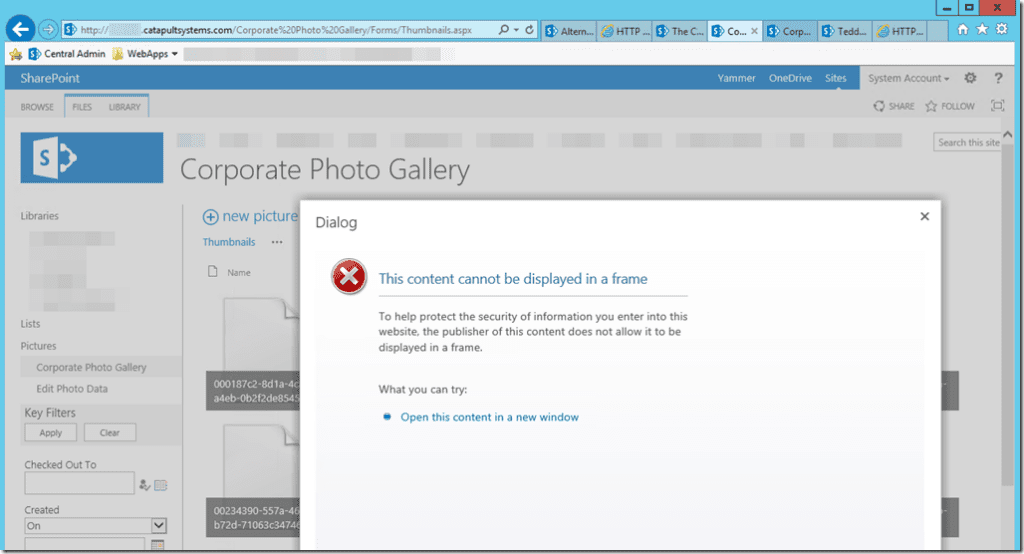
So yesterday I was creating a new Web Application in my SharePoint 2013 development environment only to see the page had timed out during it’s creation. When I refreshed the page I could see the new Web App in the list via Central Admin but when I checked IIS there was no corresponding site. It seems this wasn’t the worst part, now all of my pre-existing Web Apps were acting very strangely. Two of the Web Apps were giving a consistent HTTP 404 error, another wasn’t able to load jQuery, another would load the page but every image was replaced with a black X, and all of the pages that would pull up had randomly broken deep links.
I immediately ran Remove-SPWebApplication on the new Web App that had failed thinking this would remedy the issues I was seeing but that didn’t work. Since I noticed the 404s before any of the other symptoms I troubleshooted it like it was isolated to a single Web App:
- Verify the Loopback Check was disabled
- Verify the IP mappings in the hosts file (C:\Windows\System32\drivers\etc\hosts)
- Verify the App Pools were not stopped
- Verify the bindings on the IIS sites
- Stop/Restart the SP Timer and Administration Services
- Dismount/Mount the Web App Content DBs
- Clear the SP Config Cache (https://spcachecleaner.codeplex.com/)
In between these steps multiple IISRESETs and rebooting the server didn’t help either. I was at a loss so I started back at square one. I tried to create a new Web App, which failed again but now was at least giving me a correlation ID. Here was the ULS exception:
DocumentSet FeatureActivating: throws exception: This page has encountered a critical error. Contact your system administrator if this problem persists.. Stacktrace:
at Microsoft.SharePoint.ApplicationRuntime.SafeControls.IsSafeControl(Boolean isAppWeb, Type type, String& unsafeErrorMessage)
at Microsoft.SharePoint.WebPartPages.TypeCache.CheckIfSafeControl(Type type, Boolean isAppWeb)
Around the same time I realized the other Web Apps were also displaying strange issues.
Solution
After seeing this my focus shifted to IIS as the culprit. Rather than troubleshoot each site separately I just ran the following stsadm command to reprovision all of the SharePoint IIS sites:
stsadm -o provisionservice -action start -servicetype spwebservice
Voilà, 15 mins later everything was back to normal!

;)