Microsoft Defender for Cloud provides recommendations on various items related to Azure resources (and on-prem resources via ARC). For example, one of the recommendation types focused on vulnerabilities that may exist on virtual machines (VMs). Microsoft provides two built-in vulnerability assessment solutions for VMs.
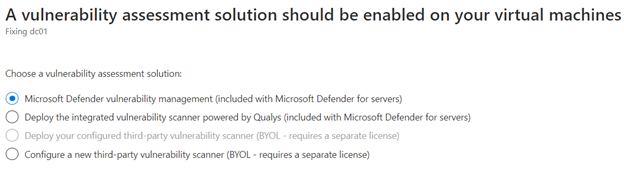
One is “Microsoft Defender vulnerability management,” and the other is the “integrated vulnerability scanner powered by Qualys” (referred to from here forward as “Qualys”). Microsoft includes both solutions as part of Microsoft Defender for Servers. In addition, Microsoft has made “Microsoft Defender vulnerability management” (referred to from here forward as “Default”) the default vulnerability scanner. These two options are shown below in Figure 1.
Figure 1 : Vulnerability assessment solutions currently available
My recommendation?
I recommend using the Qualys scanner instead of the Default vulnerability scanner. This is because the Qualys scanner looks for more vulnerabilities, resulting in a more complete result.
If you want to go further into the weeds from what I found, feel free to continue reading through the functional comparison, FAQ, and Reference Links sections below.
Functional comparison:
- When comparing a similar system in both scanners, the Qualys scanner identified significantly more vulnerabilities than the Default scanner.
- The Default scanner currently focuses only on software updates. At the same time, the Qualys scanner also identifies items such as null sessions, built-in guest accounts, Windows Explorer autoplay, and cached login credentials.
- In my example, the Qualys scanner found 8x as many vulnerabilities for a similar domain controller compared to the Default scanner.
- Both solutions are included in Microsoft Defender for Servers, so they currently have no cost difference.
FAQ’s:
- Do these scanners identify the same vulnerabilities? While there is some level of overlap in the vulnerabilities identified, they appear to be scanned using a different database for vulnerabilities.
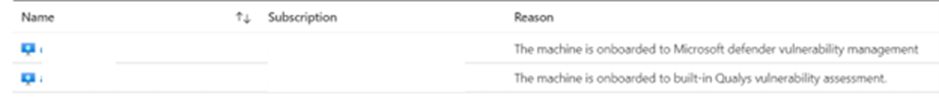
- Can you use both vulnerability scanners on a single system? Unfortunately, only one vulnerability scanner can be installed at a time on a system. However, one vulnerability scanner can be used and then removed and replaced with the other vulnerability scanner. An example of these scanners and what they look like after deployment is shown in Figure 2.
Figure 2 : Two machines with one onboarded to each vulnerability scanner.
- Do the scanners use the same vulnerability identifier? Each scanner uses a different naming convention Default uses letters such as “QXCJCS,” versus Qualys, which uses numbers such as “90044”.
- Does using one scanner versus the other impact the secure score? Having either vulnerability scanner is considered acceptable to meet the “Machines should have a vulnerability assessment solution” requirement. However, the various vulnerabilities found by each scanner also need to be resolved to increase the secure score. So the more comprehensive scanner (Qualys) will require more work to remediate the issues identified and improve the secure score.
- Is there a way to see a complete list of what each scanner assesses? Unfortunately, I could not find a way to get a complete list of what each scanner checks. I attempted to find this data through searching with Kusto but was unsuccessful. (hint, search for securityresources | where type =~ “microsoft.security/assessments/subassessments”) .
- When was this assessment performed? I performed this evaluation on the week of 1/23/23.
Reference links:
Qualys usage is included per this article: Defender for Cloud’s integrated vulnerability assessment solution for Azure, hybrid, and multicloud machines | Microsoft Learn
So, what is your experience with these options? Do you have any insights that you can provide? Please feel free to reach out to me with them on LinkedIn or Twitter!

;)